By GlavPost.com
09.23.2014
Translated and Edited by Voices of Ukraine
A paratrooper from Pskov has fully documented the movement of Russian military equipment across the Ukrainian border and the participation of Russian and Chechen servicemen in the war with Ukrainians.
In the social networks, more evidence appeared that Russian troops are fighting in Ukraine. This time, writes blogger Anton Pavlushko on his Facebook page, a Russian soldier has posted photos on social networks in which the movements of Russian troops on the territory of Ukraine can be seen, reports Obozrevatel [Observer].
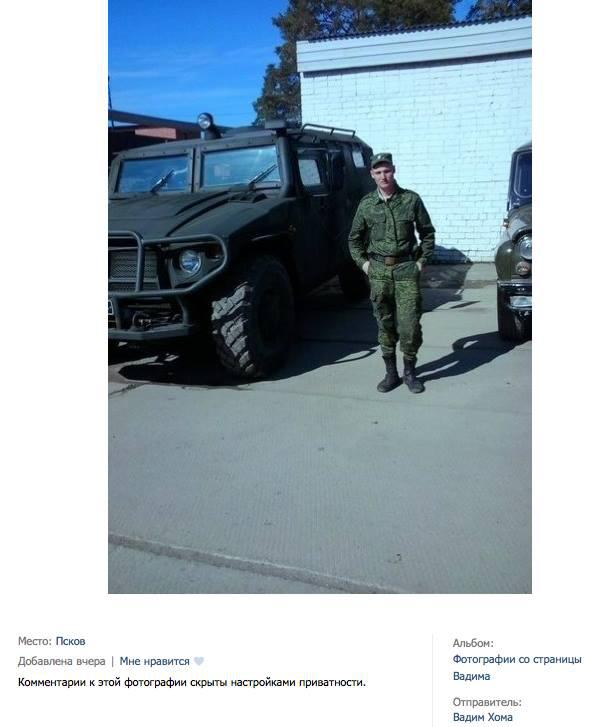
“Sooner or later, it had to come to the surface. Killers return home and begin to put out evidence of their atrocities in Ukraine. Here is Vadim Khoma, 23, from Pskov. He recently returned from Ukraine, as he reported to his readers: home !!!” –writes Pavlushko.
As the blogger notes, it may very well be that “Vadim Khoma” is just an alias, because it is the nickname of a soldier in the social network “VKontakte:” “dmirsaev” = D. Mirsaev or D. Mirzaev. The profile is clearly not new, having been active since 2013.
“Khoma/Mirzaev has not been home for a long time and decided to post his photos with comments. Apparently, he always has an iPhone and small resolution photographs that are inverted.” –said Pavlushko.
The first two photos are from Russian Donetsk. These are the vehicles ready to go into Ukraine at any moment.
Next come the photos from Ukraine signed “there, already near Dolzhansky.”
“We continue on from Dolzhansky in the Sverdlovsk region, Ukraine:
“Near Dolzhansky! And then Luhansk and Donetsk!! and then RUSSIA!!” – Commented the soldier on the photo:
Then the soldier publishes a photo from the Savur Mohyla with the comment: “a gift from the Ukrov [slang for bloody Ukrainians]!! near the Savur-Mohyla”:
He also published a photo with the words: “There are also ‘guys from Chechnya’ there :)))”
Next, a Russian soldier is photographed against the background of graffiti in a Ukrainian village: 28th OMBR [Separate Mechanized Brigade] settlement. “It was photographed long ago, and finally appeared on the Internet :))),” –writes Khoma:
Later he posts the photo, pointing out that it was taken in the Shakhtarsk Raion [district]. “The guys from the Checkpoint North,” adds the Pskov paratrooper.
Following that, in his profile is a picture of a murdered Ukrainian soldier with the following comment: “This is the militia’s handywork, we got here later. Total of 35 Ukrov killed, 3 captured, Rusych [a Russian sabotage and reconnaissance unit] worked here… why do they even need us?”
“I won’t post the photography, it’s all too graphic,” says the Ukrainian blogger.
Also, the Russian soldiers posted a photo that shows various tools, cutters, and knives, with the comment: “And now to the Stanytsia-Luhanska region,”here’s what we’re bringing with us against the Ukrov :)).”
“And so that no one says that this is a fake web account and the author forged everything, I’m posting screenshots of his photographs and account in the VKontakte website – Here’s a hero from Pskov, be it Khoma or Mirzaev,” – summed up the blogger Anton Pavlushko.
[Translator’s Note: “VKontakte” has proven to be a source of evidence for many documented war crimes as well as the presence of Russian troops in Ukraine].
Source: Glavpost.com